Think of end-to-end encryption (E2EE) like sending a valuable package in a locked box. You put the item inside, lock it, and send it off. The only person who can open it is the recipient, because they have the one and only key. Anyone who intercepts the box along the way just sees a sealed container—the contents are completely hidden.
That’s the essence of end-to-end encryption. It’s a method of securing communication that scrambles data at its source and only unscrambles it once it reaches its final destination. No one in the middle can peek inside.
Your Restaurant Data, Sealed in a Digital Vault
In the restaurant business, every tap, swipe, or online order is packed with sensitive customer data. Protecting that information isn’t just a good idea; it’s fundamental to earning customer trust and protecting your reputation. This is where E2EE steps in, acting as a digital vault for every single transaction.
When a customer pays with a TackOn Table mobile POS, their card details are instantly encrypted right at the terminal. That information is turned into a complex, unreadable code before it ever leaves the device.
From there, the scrambled data travels through your restaurant's network and across the internet, completely locked down until it arrives at the authorized payment processor. They are the only ones holding the special "key" required to unlock it and process the payment.
End-to-end encryption guarantees that data is protected from the moment of capture until it’s safely processed. This means no one—not a hacker, not your internet provider, and not even us at TackOn Table—can see the sensitive cardholder details while they're in transit.
This approach is a world away from basic transport-level encryption, which might protect data on its journey but could leave it exposed on intermediate servers. With E2EE, the information is sealed shut from start to finish.
Why E2EE Became the Gold Standard for Restaurant POS Security
The need for this level of security became crystal clear after major privacy breaches showed just how easily unencrypted communications could be intercepted. In response, E2EE emerged as the benchmark for true digital privacy, making sure that only the sender and the intended recipient can ever access the content. The E2EE market has been growing steadily ever since, as more businesses recognize its importance. You can explore more insights on the growth of the E2EE market.
For your restaurant, café, or food truck, using a system with built-in E2EE brings some serious advantages:
- Ironclad Data Security: It dramatically reduces the risk of a data breach. Even if hackers intercept the data, it's just a meaningless jumble of code to them.
- Enhanced Customer Trust: When customers know their payment information is locked down with the strongest security available, their confidence in your establishment skyrockets.
- Simplified Compliance: E2EE significantly eases the burden of meeting tough industry rules like PCI DSS, which can save you a lot of time, stress, and money.
By choosing a modern restaurant POS like TackOn Table, you're not just getting a system for taking orders and payments. You're building your business on a foundation of affordability, simplicity, and adaptability that protects both you and your customers.
E2EE Core Concepts At A Glance
To break it down even further, here are the fundamental ideas behind end-to-end encryption and what they mean for your restaurant's security.
| Concept | Description | Why It Matters For Your Restaurant |
|---|---|---|
| Encryption at the Source | Data is scrambled into ciphertext the instant it's captured (e.g., at the card reader). | Prevents sensitive card data from ever being present in a readable format on your POS or network, drastically cutting your risk. |
| Decryption at the Destination | Only the authorized endpoint (the payment processor) has the key to decrypt and read the data. | Ensures that even if data is intercepted during transit, it remains completely useless to thieves. |
| Secure Key Exchange | A secure process allows the endpoints to agree on encryption keys without exposing them. | This is the "magic" that ensures only the right recipient gets the key, keeping the entire process private. |
| No Intermediary Access | The data remains encrypted as it passes through all intermediary systems (e.g., servers, routers). | Your service providers, including us, cannot access the raw payment details, adding another critical layer of security and privacy. |
In short, these principles work together to create a secure tunnel that protects your customers' payment information from the point of sale all the way to the bank.
How End-to-End Encryption Actually Works in Café Management Software
Let's break down exactly what happens when a customer pays at your restaurant. Think of it like a super-secure armored car service for your data. Anyone can put a locked cash box in the truck, but only the bank at the final destination has the key to open it.
That’s the basic idea behind the cryptographic process. It all comes down to a matched pair of digital keys: a public key and a private key.
- The public key is like an open, unbreakable lockbox. You can give it to anyone, and they can use it to secure information by placing it inside and snapping it shut.
- The private key is the one-and-only key that can open that specific lockbox. This key is kept secret and guarded by the recipient—in this case, the payment processor.
The Journey of an Encrypted Payment
When a customer taps their card at a TackOn Table mobile POS, this whole security process unfolds in the blink of an eye. The card reader itself is the starting "end" of the journey.
-
Encryption at the Source: The instant the card reader captures the payment details, it uses the payment processor's public key to scramble the data into an unreadable code known as ciphertext. This happens right there on the device, in milliseconds.
-
Secure Transit: This encrypted block of data then travels from your POS, over your restaurant's Wi-Fi, and across the internet. During this entire trip, it’s nothing more than a jumble of useless characters. If a hacker happened to be snooping on your network, all they would see is gibberish.
-
Decryption at the Destination: The ciphertext finally arrives at the payment processor's secure servers—the final "end" of its journey. Only here is the corresponding private key used to unlock the information and safely process the transaction.
This locked-down process means that from the moment the card is read until it reaches the processor's vault, the sensitive cardholder data is never exposed in a readable format.
Why This Isn't Just Standard Encryption
You've probably seen the little padlock icon in your web browser, which signifies transport-level encryption (like HTTPS). That's good—it protects data while it's in transit over the internet. But it has a crucial weakness: intermediate servers can often see the data in plain text.
End-to-end encryption closes this security gap. Since the data is locked at the source and can only be unlocked at the final destination, any server in the middle is just passing along a sealed, unreadable package. It completely removes the "middle-man" risk.
A system this secure depends on an ironclad encryption key management policy to protect the keys themselves. Fortunately, secure café management software like TackOn Table handles all this complexity behind the scenes. You get the peace of mind that comes with top-tier security without needing a degree in cryptography. Our easy setup and built-in protocols mean your business and your customers are protected from day one.
Why Ironclad Security for Your Restaurant POS Isn't Optional
In the restaurant business, your reputation is everything. It’s built on great food, fantastic service, and the trust of your customers. A single data breach can wreck that trust in a heartbeat, leading to crippling fines and a long, painful road to recovery.
This is why understanding end-to-end encryption isn't just for the IT crowd anymore. It’s essential knowledge for anyone running a modern restaurant, café, or food truck.
Think of E2EE as your first and best line of defense. It guarantees that sensitive customer information—especially payment data—is locked down from the moment a card is swiped on your POS until it safely reaches the payment processor. This isn’t a nice-to-have feature; it's the bedrock of a secure, trustworthy business.
For restaurant owners, the peace of mind is immediate. By choosing a system with E2EE built-in, you’re not just protecting customer data. You’re protecting your reputation and dramatically cutting the risk of a security incident that could shut you down.
From Card Swipe to Secure Vault: How It Works
So, what does this process actually look like? The journey of an encrypted payment is a great way to see the power of E2EE in action. This visual breaks down how the data stays protected at every single step.
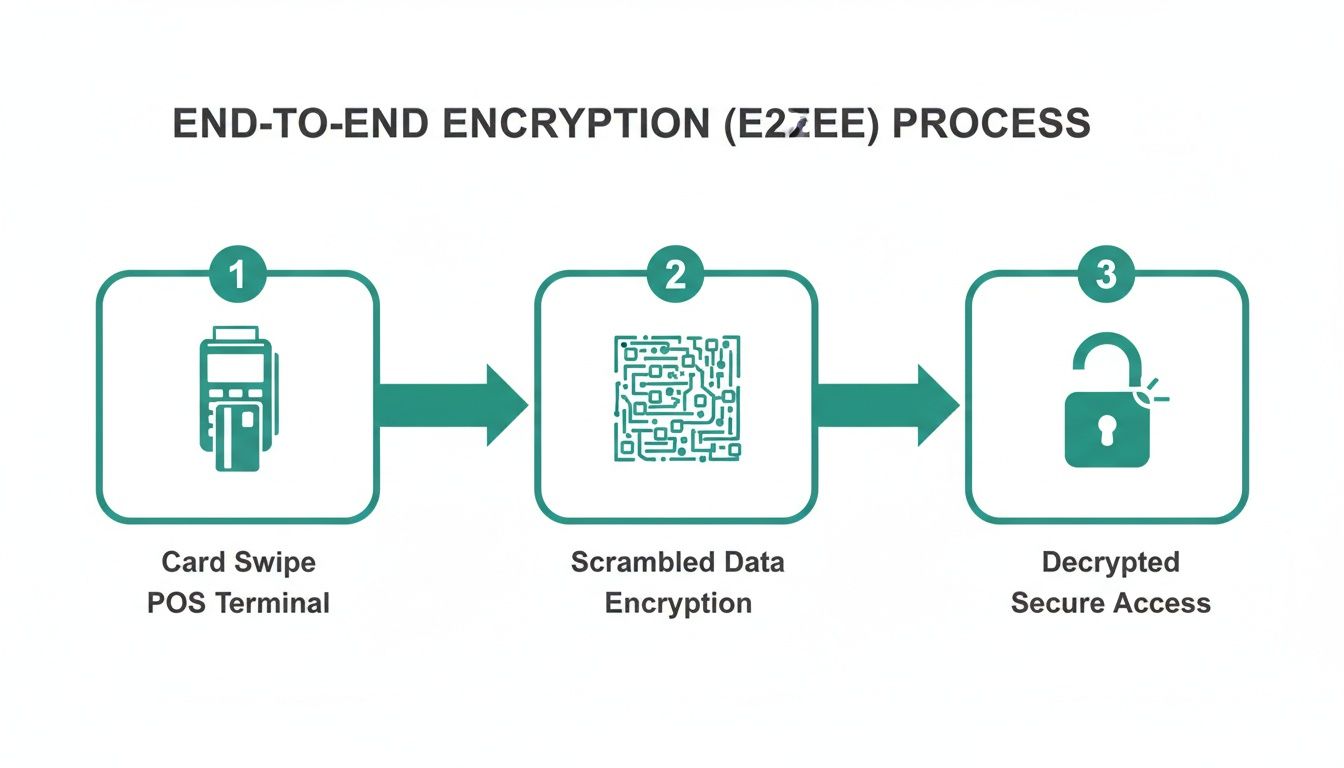
As you can see, the card details are instantly scrambled into unreadable code right at the terminal. This makes them completely useless to anyone who might try to intercept them as they travel through your network.
This built-in security is a core part of TackOn Table's approach. Our system handles this complex encryption process automatically, which means sensitive card data is never stored in a readable format on your tablets, local network, or servers. This not only provides maximum protection but also makes your life much easier when it comes to Payment Card Industry (PCI) compliance. You get to focus on serving amazing food, not deciphering complex security rules.
Encryption Methods In POS Systems A Security Comparison
Not all encryption is created equal. Many systems claim to be "secure" but offer very different levels of protection. This table breaks down how E2EE stacks up against other common methods you'll find in restaurant POS software.
| Security Feature | End-to-End Encryption (TackOn Table) | Transport Layer Security (TLS/HTTPS Only) | No Encryption at Rest |
|---|---|---|---|
| Data Protection Point | From the card reader to the payment processor. | Only during transit between two points (e.g., POS to server). | Data is unprotected when stored on local devices or servers. |
| Vulnerability Window | Minimal. Data is almost never exposed in a readable format. | Data is exposed and readable on the POS terminal and internal servers before and after transit. | Data is constantly exposed and highly vulnerable to theft. |
| PCI Compliance Scope | Significantly reduced. The POS system is out of scope. | More complex. The entire network handling the data is in scope. | Fails PCI compliance. Creates massive liability for the business. |
| Best For | Any business handling sensitive payment information. | General web browsing, but insufficient for secure payment processing alone. | No business. This is an unacceptable security risk. |
The takeaway is clear: E2EE offers a fundamentally more secure architecture, closing security gaps that other methods leave wide open. It’s the gold standard for a reason.
Why Is Everyone Talking About Encryption Now?
The move toward E2EE isn't just a trend; it's a global response to a sharp increase in cyber threats and much stricter data privacy laws. These pressures have pushed E2EE from a niche technology to an absolute must-have for businesses of all sizes.
In fact, enterprise encryption adoption has hit all-time highs. One Ponemon Institute survey revealed the largest increase in deployment in over a decade, with a major focus on databases and applications. This is happening because boards are paying attention and new laws in 144 countries now cover the vast majority of the world's population. You can read more on emerging compliance trends.
This shift makes your choice of a POS system more critical than ever. A system that cuts corners on security puts your entire operation on the line.
Protecting Every Part of Your Restaurant
A secure payment system is just the starting point. Real protection covers your entire operation, whether you're running a single food truck or a growing chain of restaurants. This is especially true for busy environments like full-service restaurants, where your team is constantly on the move and taking payments right at the table.
TackOn Table was built for this reality. Our platform doesn't just secure payments. It also gives you powerful tools for multi-location control, so you can manage user permissions, update menus, and monitor sales across all your locations from one secure place.
With TackOn Table, you get a system where powerful security works hand-in-hand with operational efficiency. Our easy setup means you’re protected from day one, without needing a dedicated IT team to manage it.
By building E2EE directly into a flexible and easy-to-use platform, we give you the confidence to grow your business knowing that your data—and your customers' data—is always protected.
Making Payment Compliance Way Easier with E2EE
Let's be honest, navigating payment security rules can feel like a nightmare. For anyone running a restaurant or café, the biggest hurdle is the Payment Card Industry Data Security Standard (PCI DSS). It’s not optional—if you take cards, you have to comply. But getting there can be a complex, expensive, and time-sucking ordeal.
This is exactly where end-to-end encryption (E2EE) becomes your secret weapon. When your POS system has true E2EE built-in, it completely flips the script on PCI compliance, making the whole thing simpler and taking a huge weight off your shoulders.
How E2EE Shrinks Your PCI Headaches
The whole point of PCI DSS is to protect customer card data wherever it’s stored, processed, or passed along. If any of your systems see that data in a readable format, they’re considered "in scope" for a PCI audit. That means they have to meet a long, painful list of security requirements.
A POS with real E2EE, like TackOn Table, scrambles card data the moment it's swiped, dipped, or tapped. The data stays encrypted as it travels through your network, which means your tablets, terminals, and Wi-Fi are never actually touching the sensitive stuff.
This is what we call scope reduction. Because the sensitive data is never exposed in your restaurant's environment, E2EE essentially shifts the burden for meeting those tough PCI rules from you to your payment processor.
What does that mean for you? Less time and money spent on network scans, firewall maintenance, and data storage policies. You get to focus on your food and your customers, not your IT security. Adopting end-to-end encryption is a massive step towards checking all the boxes on a comprehensive PCI DSS compliance checklist and making audits a breeze.
Going Beyond PCI: Why SOC 2 Compliance Matters
While PCI DSS is all about card data, there's another security benchmark you should know about: SOC 2 (Service Organization Control 2). A SOC 2 report is proof that a service provider—like your POS company—is serious about securely managing data to protect their clients' privacy and interests.
Think of SOC 2 as a seal of approval for a company’s overall security posture. It covers critical areas like:
- Security: Are systems protected from hackers and unauthorized access?
- Availability: Can you count on the system to be up and running when you need it?
- Processing Integrity: Is data processed correctly, completely, and on time?
- Confidentiality: Is confidential information properly protected?
- Privacy: Is personal information handled responsibly from start to finish?
When you choose a POS provider that is both PCI and SOC 2 compliant, like TackOn Table, you get an extra layer of peace of mind. It’s a clear signal that your technology partner views security as a core responsibility, not just a box to check. This makes TackOn Table a smarter pick when looking at Toast vs Clover alternatives, especially for owners who want top-notch, verified security without the usual complexity. Our all-in-one simplicity means that powerful compliance is built right in, not just an afterthought.
Ready to take security and compliance off your plate? See how TackOn Table’s built-in E2EE can protect your business from day one.
Start Your Free Trial Today
How TackOn Table Makes Secure Payments Effortless
All the theory behind end-to-end encryption (E2EE) is great, but what really matters is how it works in the middle of a chaotic dinner rush. Powerful security can't be a roadblock; it needs to be invisible, fast, and reliable. That's where we move past the technical jargon and deliver top-tier protection that works right out of the box.
Our entire approach is built on all-in-one simplicity. With TackOn Table, E2EE isn't some pricey add-on or a complicated setting you have to hunt for. It's built into the very core of our platform, protecting every single transaction from the moment a card is dipped, tapped, or swiped.

This integrated design means your café, food truck, or restaurant is equipped with the gold standard in payment security from day one. We sweat the complex details so you can focus on your food and your guests.
Going a Step Further with Payment Tokenization
Real security means protecting customer data at every step, not just during the brief moment of transaction. That's why TackOn Table pairs E2EE with another crucial technology: payment tokenization.
Think of a token as a secure stand-in for a credit card. When a customer pays, E2EE protects their card details on the way to the payment processor. Once there, the processor sends back a unique, non-sensitive token—basically a random string of characters—that represents that card.
This token is what we store, never the actual card number. It’s completely worthless to a hacker but gives you the power to:
- Offer secure card-on-file options for your regulars without the risk of holding their sensitive data.
- Simplify online ordering and repeat business, creating a smoother experience for loyal customers.
- Handle recurring payments or manage tabs with total peace of mind.
By swapping sensitive card numbers for secure tokens, we dramatically shrink your data security footprint. It’s one more way our system protects your business while making life easier.
This one-two punch of E2EE for data in motion and tokenization for data at rest gives your business a complete security shield.
Security That Keeps Up with Your Business
In a fast-moving restaurant, security can't slow you down. Your team needs to take orders and process payments in seconds, whether they're at the counter, tableside, or running a delivery out the door.
TackOn Table's mobile POS was built for this exact environment. Our handheld devices are lightweight but powerful, putting your entire POS system in your servers' hands. And yes, every single payment taken on these devices is guarded by the same uncompromising end-to-end encryption.
This allows you to confidently:
- Bust long lines during peak hours by taking payments anywhere on the floor.
- Improve table turnover by letting guests pay right at their seats.
- Extend your service to a patio, curbside pickup, or an off-site event without ever compromising on security.
Our simple setup gets your team running in minutes, and the intuitive interface means less time training and more time serving. It’s this blend of flexibility and security that makes our platform one of the best Toast vs Clover alternatives for modern restaurants. We offer a full suite of integrated restaurant software solutions designed for real-world efficiency.
Whether you're running a single beloved coffee shop or need seamless multi-location control for a growing franchise, TackOn Table delivers an effortless and secure payment experience. You get the robust protection you need, packaged in the simplicity you actually want.
Ready to see how simple top-tier security can be?
Book Your Free Demo Today
Common Questions About End-To-End Encryption
Even after getting the hang of what end-to-end encryption is, you probably have some practical questions about how it fits into the fast-paced world of running a restaurant. Let's tackle the most common ones we hear from owners of restaurants, cafés, and food trucks about using E2EE with the TackOn Table system. This FAQ should clear up any final doubts and show you the real-world value we bring to the table.
Is End-To-End Encryption Really Necessary For My Small Café?
Absolutely. There's a common myth that cybercriminals only go after the big fish. The truth is, small businesses are often seen as easier targets precisely because they’re assumed to have weaker security. A single data breach can be devastating for a small café, hitting you hard in both your bank account and your customers' trust.
End-to-end encryption isn't a luxury for big chains; it’s fundamental protection for any business that takes card payments, no matter how small. TackOn Table was built from the ground up to make this level of security affordable and accessible for everyone. Our easy setup gets you and your customers protected from day one, without needing a dedicated IT team on standby.
How Does TackOn Table Compare To Toast Or Clover On Security?
This is a fantastic question, and one every owner should ask when looking at their options. While established systems like Toast and Clover certainly have strong security, TackOn Table’s edge comes from how we combine enterprise-grade E2EE with genuine all-in-one simplicity. We’re a leading Toast vs Clover alternative for owners who want top-tier security without the usual operational headaches.
Our platform is engineered as a true all-in-one that’s incredibly easy to set up and manage, which is a huge plus for businesses that need smooth multi-location control. We deliver the same—and often better—data protection without the complex pricing or hardware lock-ins you see with other providers. This focus on making world-class security simple and affordable is what sets us apart.
Will E2EE Slow Down My Transactions During A Busy Lunch Rush?
Not in the slightest. It’s a valid concern, but modern encryption is incredibly efficient. The entire process of scrambling and unscrambling the data happens in milliseconds, completely invisible to your staff and customers.
With TackOn Table's optimized software and modern hardware, you get lightning-fast, smooth transactions that keep your lines moving. Our system was built to handle the high-volume pace of a busy restaurant, so you never have to choose between speed and security. You get both, every single time.
A secure transaction with TackOn Table is just as fast as an insecure one. The encryption is so efficient it has no noticeable impact on payment processing times, ensuring your service stays quick and fluid even during peak hours.
What Happens If My Internet Connection Goes Down?
Your data—and your sales—are still safe. We built TackOn Table for the real world, and that means dealing with the occasional internet outage. Our mobile POS devices are designed to be resilient.
If your connection drops, the system can keep taking payments by securely storing the encrypted transaction data right on the device. Once you're back online, that encrypted data is automatically and safely sent to the payment processor. This offline mode means you never miss a sale or compromise security, even when the Wi-Fi is spotty. It’s a critical feature that provides peace of mind and keeps your business running, no matter what.
Do I Need Technical Expertise To Manage This Security?
Nope, and that's the beauty of it. We believe powerful security should feel effortless. With TackOn Table, end-to-end encryption is just part of the package—it works automatically in the background. You won't find any complex settings to configure or technical jargon to decipher.
Our whole approach is built on simplicity, letting you run your business with the confidence that every payment is protected by the best security standards out there, no technical degree required. For a deeper dive into how it all works, you can always explore our comprehensive FAQs page. This lets you focus on what you do best: creating amazing experiences for your customers.
Ready to protect your business with a POS system that puts security and simplicity first? TackOn Table offers end-to-end encryption, seamless multi-location control, and an easy-to-use interface, all designed to help your restaurant thrive.
Book a Demo Today